Hi,
security scanners may rank the ciphers a ESXi host uses for encryption as weak.
It is possible to use a safe(r) set of ciphers.
The certificate for all service is the same, but you have to configure each service of its own.
Webgui https on port 443
Connect to the ESXi Hosts and open
/etc/vmware/rhttpproxy/config.xml
locate the cipherList node, if it not exists, create it
<config>
<vmacore>
<ssl>
<cipherList></cipherList>
</ssl>
</vmacore>
</config>
then set the cipherlist to
<cipherList>!aNULL:ECDHE+AESGCM:ECDHE+AES</cipherList>
restart the rhttpproxy daemon
~ # /etc/init.d/rhttpproxy restart
CIM daemon on port 5989
open
/etc/sfcb/sfcb.cfg
and replace the sslCipherList line with
sslCipherList: ECDHE+AESGCM:ECDHE+AES
at the end of the file. Restart the daemon
~ # /etc/init.d/vmware-fdm restart
Fault Domain Manager (HA Agent) on port 8182
open the file
/etc/opt/vmware/fdm/fdm.cfg
and add
<config>
<vmacore>
<ssl>
<cipherList>!aNULL:ECDHE+AESGCM:ECDHE+AES</cipherList>
</ssl>
</vmware>
</config>
Restart the fdm daemon
~ # /etc/init.d/vmware-fdm restart
And at least the I/O Filter daemon iofilterVP on port 9080
First, stop the daemon
~ # /etc/init.d/iofiltervpd stop
Then modify the /UserVars/ESXiVPsAllowedCiphers option by esxcli
Show current value
~ # esxcli system settings advanced list -o /UserVars/ESXiVPsAllowedCiphers
and set the new modes
~ # esxcli system settings advanced set -o /UserVars/ESXiVPsAllowedCiphers -s !aNULL:ECDHE+AESGCM:ECDHE+AES
Start the daemon
~ # /etc/init.d/iofiltervpd start
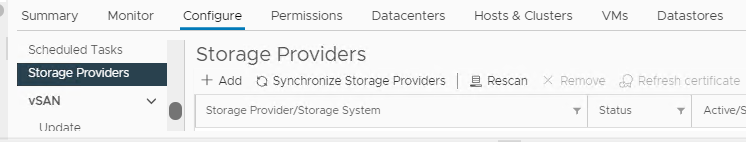
Check the state of the IO Filter Provider for this host in the vCenter’s Storage Providers list. If it is not “active” you have to reregister the hosts IO Filter Provider.
Addional hints:
Check cipher suite syntax and list allowed ciphers
openssl ciphers -v '!aNULL:ECDHE+AESGCM:ECDHE+AES'
Michael
See also
VMware vSphere 7.0 Default SSL/TLS Cipher Suites
Ciphers supported on ESX/ESXi and vCenter Server
Ciphers list