Hi,
in this post I will describe all steps to install a Windows Update Server at top an a Windows Server 2012R2 to fully support the Windows 10 Feature updates.
First of all install a Windows Server 2012R2 and install all updates. Especially KB2919355 is requiered. Windows Server2008 R2 with WSUS 3 SP2 only support Windows 10 Updates, not Features.
To install WSUS simply enable the
1 2 3 4 5 6 7 | D:\> Install-WindowsFeature -Name UpdateServices,UpdateServices-Services,UpdateServices-WidDB -IncludeManagementToolsSuccess Restart Needed Exit Code Feature Result------- -------------- --------- --------------True No Success {ASP.NET 4.5, Windows Server Update Servic...WARNING: Additional configuration may be required. Review the article Managing WSUS Using PowerShell at TechNet Library(http://go.microsoft.com/fwlink/?LinkId=235499) for more information on the recommended steps to perform WSUS installation usingPowerShell. |
Before starting the sync, 2 fixes must be installed to enable Windows 10 Feature support. Its importent to install these fixes before syncing updates otherwise all previously synced updates have to delete and you have to start resync again after installation.
Check for Update KB2919355 and install updates KB3095113 (Enable Feature Support) and KB3159706 (ESD Decryption support).
1 2 3 4 | C:\Windows\system32>systeminfo|findstr /i 2919355 [03]: KB2919355c:\> wusa Windows8.1-KB3095113-v2-x64.msuc:\> wusa AMD64-all-windows8.1-kb3159706-x64.msu |
Create a Directory where the Updates are stored
1 2 | D:\> mkdir D:\WSUSD:\> & "C:\Program Files\Update Services\Tools\WsusUtil.exe" postinstall CONTENT_DIR=D:\WSUS |
Enable WSUS and IIS Service
1 2 3 | D:\> sc config W3SVC start= delayed-autoD:\> sc config WsusService start= delayed-autoD:\> sc config WSusCertServer start= delayed-auto |
To change the default TCP Ports, a custom website must be enabled (default after installation)
1 | D:\> wsusutil usecustomwebsite true |
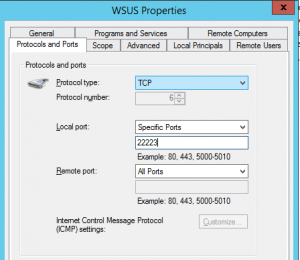
Let us assume http should be TCP/22222, then the https port must be httpPort+1 => 22223
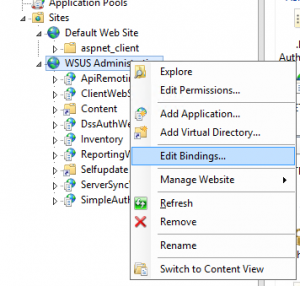
Change the IIS Ports of the customwebsite. Open the IIS Management Console
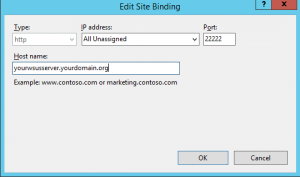
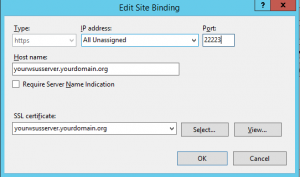
you also have to change the http port in the registry to tell the WSUSUpdate Service on which port the IIS is running.
1 | D:\> reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Update Services\Server\Setup" /t REG_DWORD /v PortNumber /d 22222 /f |
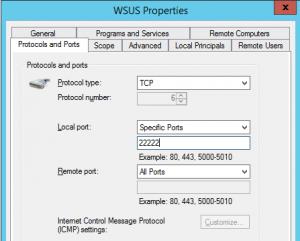
Adjust both WSUS incoming firewall rules (TCP Ports 8530=>22222 and 8531=>22223)
Reboot to get all changes active.
Addionally you have to install the Microsoft Microsoft Report Viewer to have a look at the Reports of Updates and Clients.
Start MMC and connect.
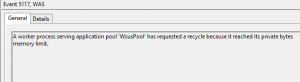
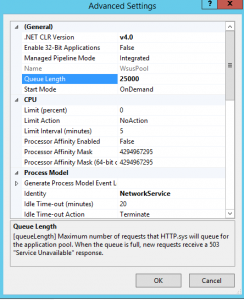
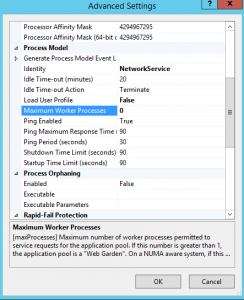
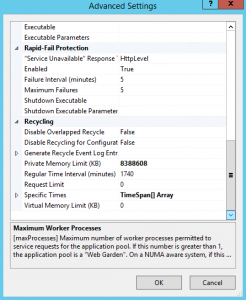
Update: If you have a large number of client which connects to your WSUS, the default settings for the IIS WSUS Apppool could be to conservative. The WsusPool then goes temporary offline. If this happens try to increase “Queue Length” and the “Private memory limit” properties of the Apppool.
To resolve the issue open System EventLog and Filter for EventSource WAS.
Increase Queue Limit
Disable worker process limit
Increase Memory limit
Also disable the SQL remote query timeout. Connect to the SQL Server and set timeout to 0 (disable timeout)
1 2 3 4 5 6 | USE SUSDB ; GO EXEC sp_configure 'remote query timeout', 0 ; GO RECONFIGURE ; GO |
otherwise in some replication scenarios a SQL timeout will occur:
SqlException: Timeout expired. The timeout period elapsed prior to completion of the operation or the server is not responding. ---> System.ComponentModel.Win32Exception: The wait operation timed out
at Microsoft.UpdateServices.DatabaseAccess.DBConnection.DrainObsoleteConnections(SqlException e)
at Microsoft.UpdateServices.DatabaseAccess.DBConnection.ExecuteReader()
at Microsoft.UpdateServices.Internal.DataAccess.HideUpdatesForReplicaSync(String xmlHiddenUpdateIds, String xmlAllUpdatesIds)
at Microsoft.UpdateServices.ServerSync.CatalogSyncAgentCore.ProcessHiddenUpdates(Guid[] hiddenUpdates, UpdateIdentity[] allUpdates)
at Microsoft.UpdateServices.ServerSync.CatalogSyncAgentCore.ReplicaSync()
at Microsoft.UpdateServices.ServerSync.CatalogSyncAgentCore.ExecuteSyncProtocol(Boolean allowRedirect)
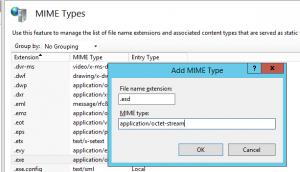
If you want to upgrade Windows 10 to a new feature version, i.e. 1511 to 1607 the IIS must known how to handle .esd files. Add the MIME Type application/octet-stream for file extension .esd to IIS by using the IIS Management Console
On the clients the Policy “User Configuration/Administrative Templates/Windows Components/Store/Turn off the offer to update to the latest version of Windows” must not be set. Check the registry key
1 2 | C:\> reg query HKLM\Software\Policies\Microsoft\WindowsStore -v DisableOSUpgrade DisableOSUpgrade REG_DWORD 0x0 |
Michael
Ref: Windows 10 Update History
Migration from WID to SQL Server