Hi,
assigning permissions in vSphere is sometimes difficult. Also to find out which permissions are missing for a specific action if you are not an administrator.
Continue reading vSphere: Find missing permissions/privileges in logs
Hi,
assigning permissions in vSphere is sometimes difficult. Also to find out which permissions are missing for a specific action if you are not an administrator.
Continue reading vSphere: Find missing permissions/privileges in logs
Hi,
This post is developed by the trial and error principle 
On Windows a User with just “normal” user rights cannot see and execute Tasks created from User with Administrator permissions. There are dozed of sites that describes that the permissions of an task can be changed by setting the filesystems rights in C:\Windows\System32\Tasks. But this won’t work since some early Versions of Windows 10 (IMHO 1607).
Continue reading Windows: Permit a limited user to run a schedule task defined by an Administrator
Hi,
in domain environments it sometimes happens that user or groups would be deleted but is still authorized on many object, i.e. filesystems, shares etc..
Continue reading Windows: Cleanup Permissions from deleted Active Directory Objects
Hi,
when it is necessary that normal user needs the ability to do some operations on a service, such as starting or stopping, multiple ways exists to grant these permissions. Windows has no GUI or (easy to use) command line tool on board to set these access rights. I will show you 3 ways to set them.
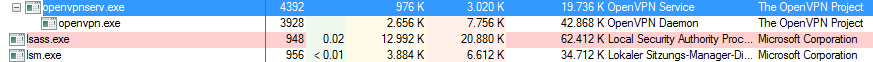
For the following examples I will use the OpenVPN Service with its Service Name openvpnservice and assign the start and stop permissions to a user or group. But its the same procedure for all other services.
The easiest way is to use the sysinternals Process Explorer. It provides a graphical user interface but has the dependency that the service must be in the running state before process explorer is started. If you already have a valid openvpn configuration start the service:
sc start openvpnservice
Then start the process explorer as administrator and locate the openvpn service process openvpnserv.exe.
Hi,
for a lot of powershell scripts Administrator permissions are necessary. In powershell, you can check if you are elevated by the following script code.
Insert the snippet at the top of your script. It checks the credentials and exits the script if the administrator permissions are missing.
Continue reading Powershell: Check for Administrator rights